Every project requires the creation of SAP Security Roles for the various Functional Tasks that are part of their ERP process. This is a laborious task and requires quite a bit of planning and coordination.
One primary task for Role Design is to list down the relevant Transaction Codes for a particular Role that you need to design.
What if I told you there is an easy way to build your Roles?
Let's say you need to build an Accounts Payable Role. You can take help from SPRO for this.
Here's how:
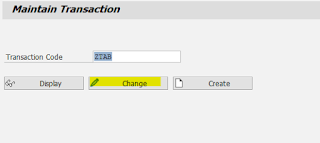
1. Tcode SPRO_ADMIN: Create a new IMG project
2. Click on 'Change Selection'
3. Select the relevant IMG Node. In our case, we will select Accounts Payable
4. Next, we need to Generate the new project
5. Now, we go to PFCG, to add this new project in a Role.
Create a new Role - Do not add anything in the Role Menu.
Go to Utilities -> Customizing Auth
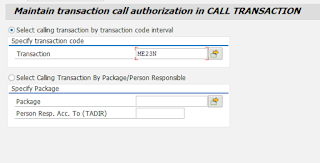
6. Select IMG Project and select the project that you created
7. The Role will be populated with all the relevant Tcodes needed for Accounts Payable.
Now you can analyze these Tcodes and modify/trim the Role according to your requirements.
One primary task for Role Design is to list down the relevant Transaction Codes for a particular Role that you need to design.
What if I told you there is an easy way to build your Roles?
Let's say you need to build an Accounts Payable Role. You can take help from SPRO for this.
Here's how:
1. Tcode SPRO_ADMIN: Create a new IMG project
2. Click on 'Change Selection'
3. Select the relevant IMG Node. In our case, we will select Accounts Payable
4. Next, we need to Generate the new project
5. Now, we go to PFCG, to add this new project in a Role.
Create a new Role - Do not add anything in the Role Menu.
Go to Utilities -> Customizing Auth
6. Select IMG Project and select the project that you created
7. The Role will be populated with all the relevant Tcodes needed for Accounts Payable.
Now you can analyze these Tcodes and modify/trim the Role according to your requirements.